Home | TCP/IP Essentials | Transport Layer | Layer 4 Ports
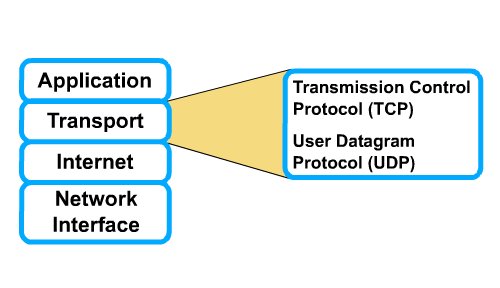
TCP and UDP - Transport layer (Layer 4) Protocols
As you know, a router has the ability to make intelligent decisions regarding the best path for delivery of data over a network. This is based on a Layer 3 or network layer addressing scheme. The router uses this information to make forwarding decisions. Once data packets go through the network layer, the transport layer, Layer 4, assumes that it can use the network as a "cloud" to send data packets from the source to the destination. The cloud resolves issues such as "Which of several paths is best for a given route?" In this Study Guide, you will start to see the role that routers perform in this process. In addition, you will learn how the transport layer regulates the flow of information from source to destination reliably and accurately.This Study Guide explains the primary functions that occur at the transport layer. This includes end-to-end control provided by sliding windows and the reliability in sequencing numbers and acknowledgments. In addition, this Study Guide describes how the transport-layer data stream is a logical connection between the endpoints of a network. Keeping this in mind, you will learn how the transport-layer data stream provides transport services from the host to the destination, often referred to as end-to-end services. In addition, you will learn about TCP and UDP and how they use port numbers to keep track of different conversations that cross the network at the same time, to pass information to the upper layers.
The phrase "quality of service" is often used to describe the purpose of Layer 4 - the transport layer. Its primary duties are to transport and regulate the flow of information from source to destination, reliably and accurately. The end-to-end control, provided by sliding windows, and reliability in sequencing numbers and acknowledgments are primary duties of Layer 4.
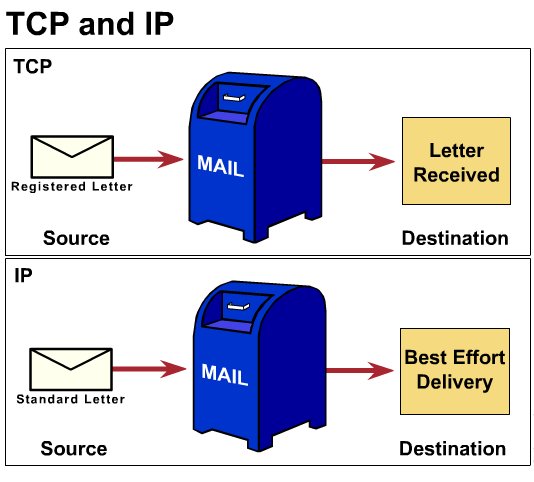
To understand reliability and flow control, think of a student who studies a foreign language for one year. Now imagine he/she visits the country where the language is used. In conversation he/she must ask everyone to repeat their words (for reliability) and to speak slowly, so he/she can catch the words (flow control). The emphasis of this curriculum is on TCP/IP Ethernet networks. The TCP/IP protocol of the OSI model Layer 4 (transport layer) has two protocols - TCP and UDP.
TCP supplies a virtual circuit between end-user applications. These are its characteristics:
- connection-oriented
- reliable
- divides outgoing messages into segments
- reassembles messages at the destination station
- re-sends anything not received
- reassembles messages from incoming segments.
- connectionless
- unreliable
- transmit messages (called user datagrams)
- provides no software checking for message delivery (unreliable)
- does not reassemble incoming messages
- uses no acknowledgments
- provides no flow control
Connection-oriented is a communications architecture that requires an establishment of the session between two nodes before transmission can begin. When the communications is completed, the session is ended (torn down). All circuit-switched networks are connection oriented because they require a dedicated channel for the duration of the session. The most ubiquitous circuit-switched network is the PSTN. In addition, packet-switched X.25, frame relay and ATM networks are also considered connection oriented, because they require receiving nodes to acknowledge their ability to support the transmission before data can be sent. Contrast with connectionless.
Following are the definitions of the fields in the TCP segment:
- source port -- number of the calling port
- destination port -- number of the called port
- sequence number -- number used to ensure correct sequencing of the arriving data
- acknowledgment number - next expected TCP octet
- HLEN -- number of 32-bit words in the header
- reserved -- set to zero
- code bits -- control functions (such as setup and termination of a session)
- window-- number of octets that the sender is willing to accept
- checksum -- calculated checksum of the header and data fields
- urgent pointer -- indicates the end of the urgent data
- option-one option -- maximum TCP segment size
- data -- upper-layer protocol data
UDP uses no windowing or acknowledgments, therefore application layer protocols provide reliability. UDP is designed for applications that do not need to put sequences of segments together. Protocols that use UDP include:
- TFTP (Trivial File Transfer Protocol)
- SNMP (Simple Network Management Protocol)
- DHCP (Dynamic Host Control Protocol)
- DNS (Domain Name System
Any conversation bound for the FTP application uses the standard port number 21.
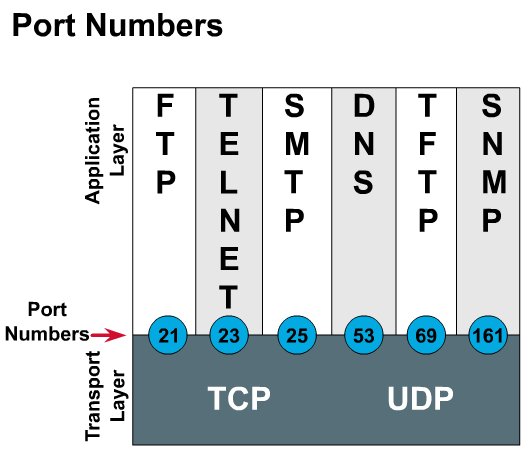
Some ports are reserved in both TCP and UDP , although applications might not be written to support them. Port numbers have the following assigned ranges:
Numbers below 255 - for public applications
Numbers from 255-1023 - assigned to companies for marketable applications
Numbers above 1023 - are unregulated
End systems use port numbers to select proper applications. Originating source port numbers are dynamically assigned by the source host; usually, it is a number larger than 1023.
Connection oriented services involve three phases. In the connection establishment phase, a single path between the source and destination is determined. Resources are typically reserved at this time to ensure a consistent grade of service. During the data transfer phase, data is transmitted sequentially over the established path, arriving at the destination in the order in which it was sent. The connection termination phase consists of terminating the connection between the source and destination when it is no longer needed.
TCP hosts establish a connection-oriented session with one another using a three-way handshake. A three-way handshake/open connection sequence synchronizes a connection at both ends before data is transferred. This exchange of introductory sequence numbers, during the connection sequence is important. It ensures that any data that is lost, due to transmission problems, can be recovered.
First, one host initiates a connection by sending a packet indicating its initial sequence number of x with a certain bit in the header set to indicate a connection request. Second, the other host receives the packet, records the sequence number of x, replies with an acknowledgment of x + 1, and includes its own initial sequence number of y. The acknowledgment number of x + 1 means the host has received all octets up to and including x, and is expecting x + 1 next. Positive acknowledgment and retransmission, or PAR, is a common technique many protocols use to provide reliability. With PAR, the source sends a packet, starts a timer, and waits for an acknowledgment before sending the next packet. If the timer expires before the source receives an acknowledgment, the source retransmits the packet and starts the timer over again.
Note: to view the demo, you will need the Macromedia Flash plugin installed in your browser. Most probably, it is already installed in your computer, but if not, You can download the player from HERE.
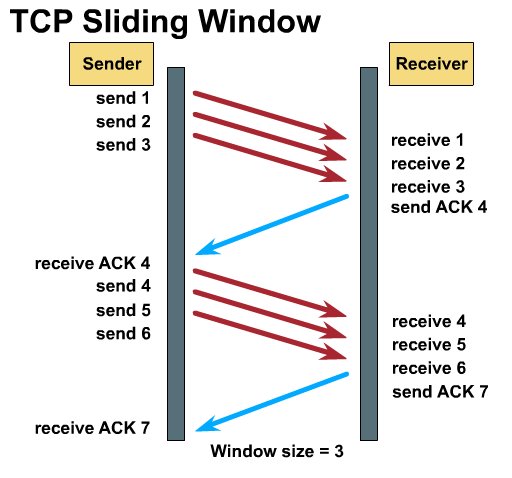
Window size determines the amount of data that you can transmit at one time before receiving an acknowledgment from the destination. The larger the window size number (bytes), the greater the amount of data that the host can transmit. After a host transmits the window-sized number of bytes, the host must receive an acknowledgment that the data has been received before it can send any more messages. For example, with a window size of 1, each individual (1) segment must be acknowledged before you can send the next segment.
TCP uses expectational acknowledgments, meaning that the acknowledgment number refers to the octet that is next expected. The "sliding" part, of sliding window, refers to the fact that the window size is negotiated dynamically during the TCP session. This results in inefficient use of bandwidth by the hosts. Windowing is a flow control mechanism requiring that the source device receive an acknowledgment from the destination after transmitting a certain amount of data. For example, with a window size of three, the source device can send three octets to the destination. It must then wait for an acknowledgment. If the destination receives the three octets, it sends an acknowledgment to the source device, which can now transmit three more octets. If, for some reason, the destination does not receive the three octets, for example, due to overflowing buffers, it does not send an acknowledgment. Because the source does not receive an acknowledgment, it knows that the octets should be retransmitted, and that the transmission rate should be slowed.
TCP provides sequencing of segments with a forward reference acknowledgment. Each datagram is numbered before transmission. At the receiving station, TCP reassembles the segments into a complete message. If a sequence number is missing in the series, that segment is re-transmitted. Segments that are not acknowledged within a given time period result in re-transmission.
In this Study Guide, you learned about the functions of the transport layer and the different processes that occur as data packets travel through this layer.
More specifically, you learned that:
The transport layer regulates information flow to ensure end-to-end connectivity between host applications reliably and accurately.
The TCP/IP protocol of Layer 4 (transport layer) has two protocols: TCP and UDP.
TCP and UDP use port (or socket) numbers to keep track of different conversations that cross the network at the same time, to pass information to the upper layers.
The three-way handshake sequence synchronizes a logical connection between the endpoints of a network.
Now that you have completed this Study Guide, you should have a firm understanding of how the transport layer provides transport services from the host to the destination, often referred to as end-to-end services.
